AWS Infrastructure for Agent-Based Payment Execution: Architecture, Stages and Reliability
An AWS architecture guide for building autonomous payment systems that scale.
The question isn't whether your agent can call a payment processor. It's whether your infrastructure can handle what happens when that call fails, times out, partially succeeds, or triggers an unexpected retry. Most agent payment systems answer this question in production. Here's how to answer it before you deploy
This guide breaks down the infrastructure components you need, why each matters, and how to architect them.
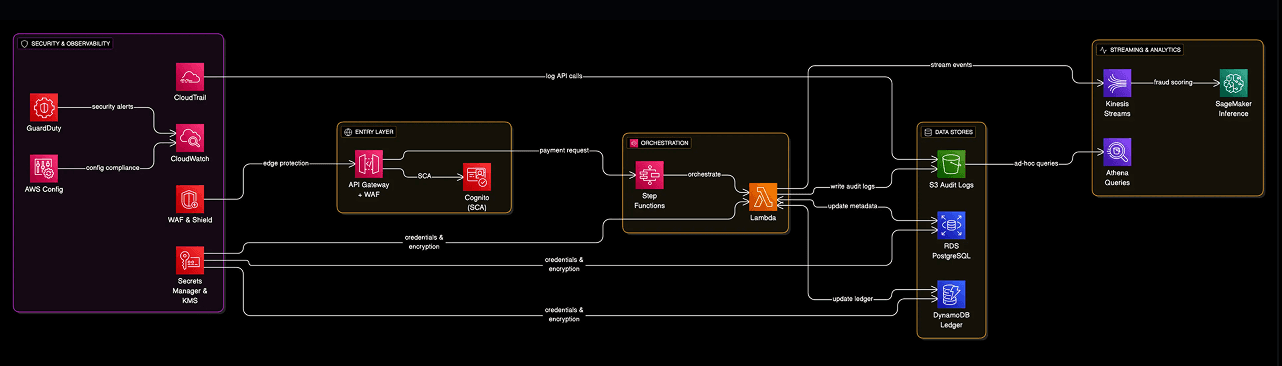
The Core Infrastructure Stack
Agent-based payment systems require seven foundational infrastructure layers. Skip any of these, and you're building on unstable ground.
1. Event-Driven Message Queue Architecture
Why it matters: Payment agents operate asynchronously. When an authorisation agent fails mid-transaction, you need guaranteed message delivery. Without proper queuing, you risk payment data loss and duplicate charges.
AWS services you need:
Amazon SQS (Standard Queues) - Your primary message transport for agent communication. Configure separate queues for different payment operations (authorisation, settlement, refunds, notifications).
Configuration:
Message retention: 4 days (enough to survive weekend outages)
Visibility timeout: 5 minutes (matches agent processing SLA)
Dead Letter Queue threshold: 3 attempts before moving to DLQ
Amazon SQS (FIFO Queues) - For operations requiring strict ordering, like settlement sequences where you must authorise before capturing.
Critical setting: Use message group IDs based on customer or transaction ID to maintain ordering per payment flow while allowing parallel processing across different customers.
Dead Letter Queues (DLQ) - Failed messages need special handling. Your DLQ should trigger alerts immediately because every message represents a stuck payment.
Amazon EventBridge - Routes events between agents without tight coupling. When a fraud detection agent flags a transaction, EventBridge notifies the authorisation agent, the customer notification agent, and your monitoring system simultaneously.
Real-world example: During Black Friday traffic spikes, your authorisation agent might process 10x normal volume. SQS automatically buffers the load while your agents scale up, preventing dropped transactions.
Cost consideration: SQS charges per request. At 1M transactions/month with 5 queue operations per transaction, expect around $2.50/month for queuing alone. Not the bottleneck.
2. Agent Orchestration & Workflow Management
Why it matters: A single payment involves 5-7 agent interactions (fraud check → authorisation → settlement → reconciliation → notification). You need orchestration that survives failures and provides visibility into where payments get stuck.
AWS Step Functions - Your orchestration engine. Models complex payment workflows as state machines with built-in retry logic and error handling.
How to structure payment workflows:
1. Fraud Detection Agent (parallel execution)
↓ if approved
2. Authorization Agent (with retry logic)
↓ if successful
3. Settlement Agent (idempotent execution)
↓ always
4. Notification Agent (best effort)
↓ async
5. Reconciliation Agent (scheduled)
State machine design pattern: Use the "saga pattern" for multi-step transactions. If settlement fails after authorisation, Step Functions automatically triggers the compensation flow to void the authorisation.
Express vs Standard workflows:
Standard workflows: Use for settlement processes that must complete (even if they take hours)
Express workflows: Use for time-sensitive fraud checks where you need sub-second latency
Timeout strategy: Set aggressive timeouts on external API calls (payment processors, banks). If Stripe doesn't respond in 3 seconds, your agent should make a decision based on available data rather than blocking the customer.
Cost reality check: Step Functions charges per state transition. A payment with 7 agent steps costs ~$0.00025 in orchestration fees. Not your cost problem.
3. Agent Runtime Infrastructure
Why it matters: Where your agents actually execute determines latency, scalability, and operational overhead. Choose wrong and you'll either overpay or struggle with performance.
AWS Lambda
When Lambda works well:
Fraud detection agents (spiky traffic, millisecond decisions)
Notification agents (fire-and-forget operations)
Webhook handlers (unpredictable volume)
Lambda configuration for payment agents:
Memory: 1024MB minimum (gives you proportional CPU)
Timeout: 30 seconds for external API calls, 5 seconds for internal operations
Concurrency limits: Set reserved concurrency to prevent runaway costs
VPC configuration: Required for accessing payment databases
Cold start mitigation: Use provisioned concurrency for your authorisation agent (the critical path). Costs more but eliminates the 500ms-2s cold start delay.
Amazon ECS Fargate - For agents requiring persistent connections or complex dependencies.
When containers make sense:
Settlement agents processing continuous streams
ML-based fraud agents with large model files
Agents integrating with legacy SOAP services
Container sizing: Start with 0.5 vCPU, 1GB memory. Payment agents are usually I/O bound (waiting on databases and APIs) rather than compute bound.
Amazon Bedrock - Your AI agent runtime for sophisticated reasoning tasks.
Use cases in payments:
Fraud pattern detection beyond rule-based systems
Payment routing optimisation (choosing fastest/cheapest processor)
Dispute resolution triage
Exception handling for failed transactions
Model selection:
Claude Sonnet: Complex reasoning for fraud analysis and dispute handling
Claude Haiku: Fast, cost-effective for payment categorisation and routing
Bedrock guardrails you must enable:
PII detection (prevent card numbers in prompts)
Content filtering (block injection attacks)
Custom validation (ensure agents stay within payment domain)
Cost control: Set per-agent token limits. A fraud agent shouldn't consume 10,000 tokens analysing a $5 transaction.
4. State Management & Data Persistence
Why it matters: Payment systems require tracking complex state across multiple agents while maintaining ACID guarantees for financial operations. Explore further here: AWS Infrastructure for Agent-Based Payment Systems: State, Idempotency and Failure Handling
Your data architecture must handle both high-throughput transactions and complex audit queries.
Amazon DynamoDB - High-speed transaction state tracking.
Table design for payments:
Transactions table:
Partition key:
transaction_idSort key:
timestampGSI:
customer_id-timestamp(for customer transaction history)TTL: Remove completed transactions after 90 days (move to S3)
Why DynamoDB for payment state:
Single-digit millisecond latency
Automatic scaling to millions of transactions
Built-in encryption at rest
Point-in-time recovery for disaster scenarios
Capacity planning: Use on-demand mode initially. At 100K transactions/month, you'll pay around $25-30/month. Switch to provisioned capacity once traffic patterns stabilise. Check Amazon Web Services pricing prices as these may change.
Idempotency table:
Partition key:
idempotency_keyAttributes:
transaction_id,result,created_atTTL: 24 hours (clients must retry within this window)
This prevents duplicate charges when clients retry failed requests.
Amazon RDS PostgreSQL - Complex queries and compliance reporting.
What goes in RDS:
Payment history requiring joins (customer + transaction + merchant)
Accounting reconciliation data
Compliance audit trails
Business intelligence queries
Schema design:
Use JSONB columns for flexible agent metadata
Partition tables by month (payments_2026_01, payments_2026_02)
Maintain read replicas in different AZs
Backup strategy: Automated daily snapshots with 35-day retention (regulatory requirement). Point-in-time recovery enabled.
Amazon ElastiCache (Redis) - Agent session management and hot data.
What I cache:
Customer fraud scores (update every 5 minutes)
Payment processor availability status
Rate limiting counters
Agent decision metrics
TTL strategy:
Fraud scores: 5 minutes
Processor status: 1 minute
Rate limits: 1 hour sliding window
Cost optimisation: Use cache.t3.micro for dev/staging (\(13/month), cache.r6g.large for production (~\)150/month). Cheaper than repeated database queries.
5. Security & Compliance Infrastructure
Why it matters: Payment systems handle the most sensitive data in your organisation. Security failures lead to regulatory fines, loss of payment processor relationships, and potentially business closure.
AWS KMS - Encryption key management for payment data.
Key architecture:
Separate KMS keys per environment (dev/staging/prod)
Separate keys for different data classifications (PII, PCI, general)
Key rotation enabled (automatic annual rotation)
Encryption strategy:
DynamoDB: Encrypt tables with KMS
RDS: Encrypt database and snapshots
S3: Encrypt audit logs and archived transactions
SQS: Encrypt messages in transit and at rest
AWS Secrets Manager - Secure storage for API keys and credentials.
What belongs in Secrets Manager:
Payment processor API keys (Stripe, Adyen)
Database credentials
Third-party API tokens
Webhook signing secrets
Rotation policy: Rotate payment processor credentials every 90 days. Automate rotation using Lambda functions.
Amazon VPC - Network isolation for payment processing.
VPC architecture:
Public subnets: API Gateway, ALB only
Private subnets: All payment agents, databases
Isolated subnets: PCI-sensitive operations (tokenisation)
Security group strategy:
Agent security group: Allow outbound to payment processors only
Database security group: Allow inbound from agent security group only
No direct internet access for agents (use NAT Gateway)
AWS WAF - Protection against API abuse and injection attacks.
Rules I always enable:
Rate limiting (100 requests/minute per IP)
SQL injection protection
Cross-site scripting (XSS) filters
Geographic restrictions (block high-risk countries if applicable)
Custom rule: Block requests with credit card patterns in URLs or headers (prevents accidental PCI violations).
VPC Endpoints - Keep AWS service traffic private.
Critical endpoints for payment systems:
DynamoDB endpoint (prevent database traffic leaving VPC)
S3 endpoint (for audit log uploads)
Secrets Manager endpoint (credential retrieval)
KMS endpoint (encryption operations)
Security benefit: Even if an agent is compromised, payment data never traverses the public internet.
6. Observability & Monitoring Infrastructure
Why it matters: Payment systems fail silently. By the time customers complain, you've already lost revenue and damaged trust. Comprehensive monitoring catches issues before they impact business metrics.
Amazon CloudWatch - Centralised logging and metrics.
Custom metrics I track:
Payment success rate (target: >99.5%)
Authorisation latency P99 (target: <800ms)
Agent error rate by type (fraud, auth, settlement)
DLQ message depth (alert if >10)
Cost per transaction (track unit economics)
Log groups structure:
/aws/lambda/fraud-detection-agent
/aws/lambda/authorization-agent
/aws/lambda/settlement-agent
/aws/stepfunctions/payment-orchestration
/aws/apigateway/payment-api
Log retention:
Production: 30 days in CloudWatch, then archive to S3
Compliance logs: 7 years in S3 Glacier
CloudWatch Alarms:
Critical alarms (page on-call):
Payment success rate drops below 99%
Authorisation latency P99 exceeds 1 second
Any DLQ receives messages
Settlement agent error rate exceeds 0.5%
Warning alarms (Slack notification):
Cost per transaction increases 20%
Agent invocation count spikes 3x normal
Database connection pool exhaustion
AWS X-Ray - Distributed tracing across agents.
Why tracing matters: When a payment fails, you need to see the complete journey: API Gateway → Step Functions → Fraud Agent → Auth Agent → External Processor.
Trace all payment flows: Enable X-Ray on Lambda, API Gateway, and Step Functions. The cost ($5 per million traces) is negligible compared to debugging time saved.
Service map insights: X-Ray automatically generates visual maps showing which agent is the bottleneck. Usually it's the external payment processor, not your code.
Amazon SNS - Critical alert distribution.
Topic structure:
payment-critical-alerts→ PagerDuty integrationpayment-warnings→ Slack channelpayment-metrics→ Metrics dashboard updates
Alert content must include:
Affected transaction ID
Error type and message
Runbook link for remediation
Customer impact estimate
AWS CloudTrail - Complete audit trail of infrastructure changes.
Why this matters for payments: Auditors will ask "who modified the fraud detection configuration on November 15th?" CloudTrail provides the answer with timestamps and identity proof.
Events to monitor:
IAM role changes affecting payment agents
Security group modifications
KMS key policy updates
Lambda function code deployments
7. Data Archival & Analytics Infrastructure
Why it matters: Payment data has long-term value for business intelligence and regulatory compliance. Your architecture must support both hot operational data and cold analytical storage.
Amazon S3 - Long-term transaction storage.
Bucket structure:
payment-archives/
├── transactions/year=2026/month=01/
├── audit-logs/year=2026/month=01/
└── reconciliation-reports/year=2026/month=01/
Lifecycle policies:
0-90 days: S3 Standard (frequent access for support queries)
90 days-2 years: S3 Infrequent Access (occasional compliance checks)
2-7 years: S3 Glacier (regulatory retention requirement)
Compliance requirement: PCI DSS mandates retaining transaction logs for at least 1 year, longer for some jurisdictions.
Amazon Athena - SQL queries on archived transaction data.
Use cases:
"Show all transactions over $10K in Q4 2025"
"Calculate refund rates by payment processor"
"Identify unusual transaction patterns for fraud analysis"
Performance optimisation: Partition data by year/month/day. Query costs drop 10x with proper partitioning.
Amazon Redshift - Data warehouse for business intelligence.
When to add Redshift: Once you're processing 1M+ transactions monthly and finance teams request complex analytics.
Schema design:
Fact table: transactions (transaction_id, amount, status, timestamps)
Dimension tables: customers, merchants, processors, agents
Refresh strategy: Load new data from S3 daily via scheduled Glue jobs.
Infrastructure Sizing Guide by Transaction Volume
Your infrastructure needs scale with transaction volume. Here's what I recommend:
Early Stage (0-100K transactions/month)
Compute:
Lambda only (no ECS complexity yet)
On-demand pricing for everything
Provisioned concurrency: None (cold starts acceptable)
Database:
DynamoDB on-demand
RDS db.t3.small (2 vCPU, 2GB RAM)
No read replicas yet
Monthly AWS cost estimate: $200-400
Growth Stage (100K-1M transactions/month)
Compute:
Lambda with provisioned concurrency for auth agent (2 instances)
Consider ECS for settlement agent if cost matters
Reserved capacity planning begins
Database:
DynamoDB provisioned mode (25 WCU, 50 RCU)
RDS db.r5.large with read replica
ElastiCache cache.t3.small
Monthly AWS cost estimate: $800-1,500
Scale Stage (1M-10M transactions/month)
Compute:
Hybrid Lambda/ECS architecture
Auto-scaling groups for predictable workloads
Multi-region deployment planning
Database:
DynamoDB auto-scaling (100-500 WCU)
RDS db.r5.xlarge with multi-AZ
ElastiCache cluster mode (3 nodes)
Monthly AWS cost estimate: $3,000-6,000
Not sure which tier your infrastructure should be at?
The OPEX Calculator models your architecture costs across each growth stage, enter your current service count and transaction volume, get a risk and cost estimate in under 60 seconds.
Enterprise (10M+ transactions/month)
Compute:
Primarily ECS Fargate for cost efficiency
Reserved instances for base load
Lambda for spiky/unpredictable traffic
Database:
DynamoDB global tables (multi-region)
RDS Aurora with read replicas in multiple regions
ElastiCache Redis cluster (6+ nodes)
Monthly AWS cost estimate: $10,000-30,000
Cost optimisation opportunity: At this scale, negotiate enterprise discount programs with AWS (typically 10-15% off).
⚠️ The Hidden Cost Most Teams Miss
These AWS infrastructure costs are just the beginning. The real expenses come from:
Architecture mistakes that require expensive refactoring
Security misconfigurations that delay PCI compliance
Over-provisioned resources inflating monthly bills 30-50%
Team time debugging production failures
Want to compress that timeline to 6-8 weeks?
Your Architecture Review → We'll review your current infrastructure, identify critical gaps, and provide a detailed remediation roadmap
Critical Infrastructure Patterns for Reliability
Pattern 1: Circuit Breaker for External Services
Payment processors fail. Your infrastructure must handle it gracefully.
Implementation:
Track error rate for each payment processor
If error rate exceeds 5% in 1-minute window → open circuit
Route traffic to backup processor
Retry after 30 seconds (half-open state)
Why it matters: When Stripe has an outage, your circuit breaker automatically routes to Adyen without manual intervention.
Pattern 2: Idempotency at Every Layer
Idempotency keys flow through:
API Gateway (client provides key)
Lambda agents (check DynamoDB for existing result)
External processors (use their idempotency mechanisms)
Database writes (conditional updates only)
Result: Clients can safely retry any failed request without risk of duplicate charges. Explore Why Payment State Is the Hardest Problem in Distributed Systems
💡 Implementation Complexity Alert
Idempotency seems simple in theory. In practice, it requires:
Distributed locking mechanisms
Clock synchronization across regions
Race condition handling
Retry logic with exponential backoff
Teams typically spend 2-3 weeks getting idempotency right.
Pattern 3: Async Processing with Synchronous Facade
Customer experience: "Processing payment..." → 200 OK response in <1 second
Behind the scenes:
API Gateway returns immediately after queuing
Step Functions orchestrates multi-minute settlement
WebSocket or polling for status updates
Business value: Fast perceived response time even when actual processing takes minutes.
Pattern 4: Multi-Region Failover
Active-active in two regions:
Route53 health checks monitor payment API
If primary region unhealthy → automatic failover
DynamoDB global tables keep data synchronized
RDS cross-region read replicas promote to primary
Availability target: 99.99% uptime (less than 5 minutes downtime/month).
Pattern 5: Cost Attribution Tags
Tag everything:
Lambda functions:
Environment,AgentType,CostCenterDynamoDB tables:
DataType,RetentionPeriodS3 buckets:
DataClassification,ComplianceScope
Why it matters: When your CFO asks "how much does fraud detection cost per transaction?" you have the answer immediately. A business impact analysis with monthly monitoring and cloud visibility will help you stay on track.
Common Infrastructure Mistakes (And How to Avoid Them)
Mistake 1: Synchronous Agent Chains
API → Fraud Agent → waits → Auth Agent → waits → Settlement → waits
Why it fails:
Total latency = sum of all agents
Single agent failure breaks entire flow
No retry capability
Correct approach:
API → Queue → Step Functions orchestrates agents in parallel/sequence
Result: 3x faster response, graceful failure handling.
Mistake 2: No DLQ Monitoring
The silent killer: Messages fail processing, move to DLQ, and nobody notices for days.
Every DLQ message represents:
Stuck payment
Unhappy customer
Potential regulatory violation
Solution: CloudWatch alarm triggers within 1 minute of any DLQ message. On-call engineer investigates immediately.
A DLQ with messages in it means a payment is stuck right now.
If you don't have DLQ depth wired into your monitoring, you won't know until a customer calls. The Agentic Readiness Assessment checks whether your observability stack covers the failure modes that matter for agent-based payment flows.
Mistake 3: Undersized Database Connections
Symptom: Payment agents fail with "connection pool exhausted" during traffic spikes.
Root cause: RDS configured with 100 max connections, but 500 Lambda instances try to connect simultaneously.
Fix:
Use RDS Proxy (connection pooling layer)
Limit Lambda concurrency to safe level
Monitor active connections in CloudWatch
Mistake 4: No Cost Guardrails
Scenario: ML-based fraud agent starts analyzing every transaction with 50,000-token prompts. AWS bill increases from $500 to $15,000 in one month.
Prevention:
Set budget alerts at 80% threshold
Implement per-agent token limits
Use Cost Explorer to track daily spending
Our automated cost monitoring would have caught this in 24 hours.** Interested in cost guardrails for your infrastructure? [Included in architecture membership plan →]
Mistake 5: Storing Sensitive Data in Logs
PCI violation example: Lambda function logs full API responses including card numbers.
Consequences:
Immediate PCI non-compliance
Potential payment processor suspension
Regulatory fines
Solution:
Implement log sanitisation at agent level
Use CloudWatch Logs data protection policies
Regular compliance audits of log contents
Next Steps: From Architecture to Implementation
You now have the complete infrastructure blueprint. Here's your implementation roadmap:
Week 1-2: Foundation
Set up multi-account AWS organisation (dev/staging/prod)
Configure VPC with public/private subnet architecture
Enable CloudTrail and Config for compliance
Create KMS keys for data encryption
Week 3-4: Core Services
Deploy API Gateway with WAF protection
Set up SQS queues and EventBridge
Configure Step Functions for orchestration
Launch RDS and DynamoDB with encryption
Week 5-6: Agent Runtime
Deploy Lambda functions for payment agents
Configure Bedrock for AI-powered agents
Set up ElastiCache for hot data
Implement circuit breaker pattern
Week 7-8: Observability
Configure CloudWatch dashboards
Enable X-Ray tracing
Set up SNS alerts to PagerDuty
Create runbooks for common failures
Week 9-10: Testing & Validation
Load testing with production-like traffic
Chaos engineering (kill random agents)
Security penetration testing
Compliance audit preparation
Week 11-12: Production Deployment
Gradual traffic ramp (5% → 25% → 100%)
Monitor business metrics continuously
Document architecture decisions
Train support team on new infrastructure
If you're building this, you don't have to figure it out alone.
You have the blueprint. The question is whether your current infrastructure matches it.
The Infrastructure Readiness Assessment scores your AWS environment against the architecture requirements in this guide, event-driven queuing, agent orchestration, state management, observability, and security. You'll get a gap analysis mapped to the specific layers where your setup falls short, with prioritised fixes.
Takes 7 minutes. No sales call required to see your results.
Run the Infrastructure Readiness Assessment →
If you need the architecture designed, reviewed, or governed for your specific AWS environment that's what a SyncYourCloud membership is for. Members get access to the full tool suite built specifically for AWS payment environments: Infrastructure & Readiness
Infrastructure Readiness Assessment — score your AWS environment against payment architecture requirements
Agentic Readiness Assessment — validate whether your infrastructure can support agent-based payment flows
AWS Cloud Assessment — multi-dimension analysis of cost, security, and performance
OpEx Calculator — model the operational cost of your architecture decisions Payment Architecture & Compliance
PCI Gap Analysis — identify gaps against PCI-DSS controls in your current setup
Security Controls Matrix — map controls to requirements across your payment stack
Cardholder Data Flow — visualise and document data movement for auditors and acquirers
Architecture Decision Records — structured documentation your team and board can act on Agentic Payments
Agent Identity Designer — define IAM roles, boundaries, and trust policies for autonomous payment agents
Agent Payment Flow Simulator — test transaction paths before you deploy
Idempotency Safety Rails — configure retry logic and deduplication for agent-initiated payments
Agent Observability Pack — monitoring and alerting patterns for agentic payment systems
Failure Playbook Generator — documented runbooks for the failure modes that matter in payments Cost & Scaling
Infrastructure Cost Modeller — project costs across architecture variants
Spend Controls Configurator — set hard and soft limits across your AWS accounts
Scaling Roadmap — phased growth plan aligned to your transaction volume targets
Latency Analysis — identify bottlenecks in your payment processing path Every engagement includes pattern-matched analysis, documented decision records, and artefacts your team can act on immediately.
Continue reading:
The 5 Stages of Deploying Agent-Based Payment Systems — complete execution framework
AWS Bedrock vs Self-Hosted LLMs — deciding between managed and self-hosted
AWS Bedrock Payment Infrastructure: 500K Architecture Decision